Elastic Compute Cloud (EC2) provides scalable computing capacity in the AWS Cloud, which you can use to launch virtual servers, configure security and networking, and manage storage.
EC2 is a foundational service used for managing virtual instances. You can provision an EC2 instance from a pre-configured template (Amazon Machine Image – AMI) and deploy your applications into the EC instance.
EC2 Features
- EC2 Instances are grouped into families, which are designed for a specific broad type workload.
- A security group must be assigned to an instance during the creation process.
- Each instance must be placed into a VPC, an AZ, and a subnet.
- Custom launch command (bootstrapping) can be passed into the instance via “user-data”
- Encrypted key-pairs are used to manage login authentication.
- You are not billed if an instance is in a state of pending, stopping, stopped, shutting down, or terminated. EBS volumes incur charges regardless of the instance’s state.
- AWS initially used a modified version of the Xen Hypervisor to host EC2 and then switched to Amazon’s own hypervisor Nitro.
- EC2 Instance Role is an IAM role that can be assumed by an EC2 instance.
- An Instance Profile, which is a container for the roles, allows application on the EC2 instances to access the temporary credentials using the instance metadata.
- You would use Elastic Load Balancing (ELB) to distribute web traffic between web-facing EC2 instances.
Bootstrapping
- Bootstrapping is a process where instructions are executed on an instance during its launch process (only in the first launch of the boot cycle).
- By default, scripts entered as “user data” are executed with root user privileges. Therefore, you do not need the “sudo” command in the script.
- User Data can be used to run shell scripts (Bash or PowerShell) or run cloud-init directives.
- The following example starts the httpd process when an EC2 instance launches.
#!/bin/bash
yum update -y
yum install httpd -y
echo "<html><body><h1>Hello World</h1></body></html>" >/var/www/html/index.html
systemctl start httpd
systemctl enable httpd
How to Access an EC2 Instance
AWS Management Console
- configures and manages instances via a web browser
Secure Shell (SSH)
- establishes a direct secure connection to your instance
- You need to generate a key pair (a private key + a public key).
- A private key is used in your client machine and a public key is used in your EC2 instance.
EC2 Instance Connect (ECI)
- provides a simple way to connect to your Linux instances using SSH
- You need to configure every instance that will support using Instance Connect (this is a one-time requirement for each instance), and you need to grant permission to every IAM principal that will use Instance Connect.
- After setting up, you can connect your instance using Amazon EC2 console (browser-based client), EC2 Instance Connect CLI, or a SSH client.
AWS Systems Manager
- You can use many services in the “Systems Manager”
- Run Command
- Session Manager
- Patch Manager
EC2 Security Groups
- Any Change to security groups take effect immediately.
- Any number of EC2 instances can be associated with a security group.
- You can attach multiple security groups to a EC2 instance.
- Default behavior:
- All inbound traffic is blocked.
- All outbound traffic is allowed.
Private or Public Instances
- Private Instances
- Private IP is automatically allocated when an instance is launched and is used for internal communication.
- Allocated with ip-x.x.x.x.ec2.internal DNS name – only works inside AWS.
- The private IP and the domain name are unchanged during stop/starts – released when terminated.
- Public Instances
- A public IP is allocated when the machine starts and deallocated when it stops.
- A Public IPs is auto-assigned based on the subnet settings. But you can assign a public IP to an instance during the launch process.
- Elastic IP (EIP) can be allocated. It is a static IPv4 address and is not deallocated when the instance stops.
Instance Lifecycle
- Start
- Boot up OS
- Run user data (bootstrap) script
- Start Applications
- Stop
- The data is kept on the disk with EBS and will remain until the instance restarts.
- Terminate
- By default, the root device volume is also terminated.
- Hibernate
- The content in the memory (RAM) is moved to the EBS root volume.
- The EBS root volume needs to be encrypted.
- Instance RAM must be less than 150 GB.
- Instances can not be hibernated for more than 60 days.
- When an instance restarts from hibernation:
- The EBS root volume is restored to its previous state.
- The memory content is restored.
- Any processes that were running are resumed.
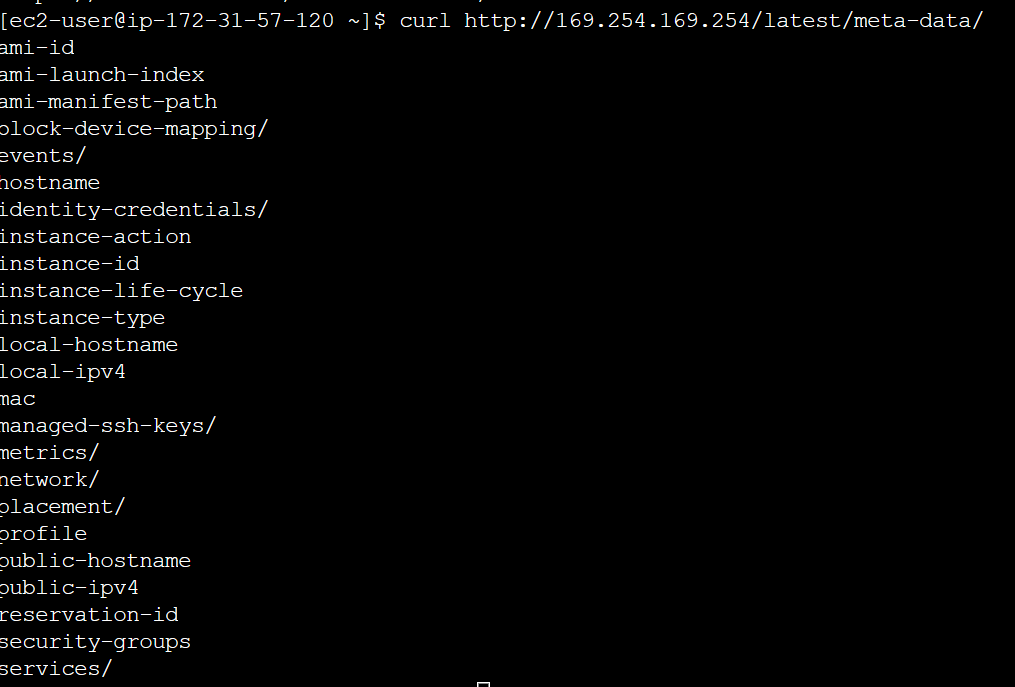
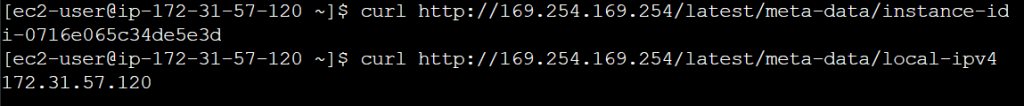
Instance Metadata
- Instance metadata is data relating to the instance that can be accessed from within the instance itself.
http://169.254.169.254/latest/meta-data/
- The metadata provides the current external IPv4 address, the availability zone, and the security group.
EBS Optimized Instances
- Legacy non-EBS-optimized instances
- Use a shared networking path for data and storage.
- EBS-optimized instances
- Use dedicated communication path for storage and data.
- Higher performance: improved network data transfer rates, fast rate of storage, higher level of consistency
EC2 Instance – Status Check
System Status Checks
- Monitor problems in AWS Systems
- Check Account Health Dashboard for any scheduled maintenance
- AWS Health Dashboard alerts you when AWS is experiencing issues that may impact you.
- You can use EventBride to handle events from AWS Health Dashboard.
- Resolution
- Stop and Restart EC2 instances
Instance Status Check
- Monitors network configuration of the instances
- Resolution
- Restart the instance
- Fix the configuration
CloudWatch Metrics
- StatusCheckFailed_System
- Power failure, network connectivity, system host issues
- StatusCheckFailed_Instance
EC2 Instance – Automatic Recovery
https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/ec2-instance-recover.html#cloudwatch-recovery
Now, the EC2 automatic recovery feature is enabled by default.
Status Check
- Instance status -> check the EC2 VM
- System status -> check the underlying hardware
Simplified automatic recovery
- Instances that support simplified automatic recovery are configured by default to recover a failed instance.
- Simplified automatic recovery is initiated in response to system status check failures.
CloudWatch action-based recovery
- You can customize when to recover your instances.
- When the StatusCheckFailed_System alarm is triggered, the recovery action is initiated.
What is recovered?
- the instance ID
- private/public IP addresses
- Elastic IP addresses
- all instance metadata
- placement group
EC2 Networking
- ENI (Elastic Network Interface)
- basic day-to-day networking
- low-cost and high-availability solution
- ENA (Enhanced Networking Adapter)
- Single root I/O virtualization (SR-IOV) for high performance (10~100 Gbps) and lower CPU utilization
- EFA (Elastic Fabric Adapter)
- For High Performance Computing (HPC) and Machine Learning
IP Addresses
- Public IP Address
- lost when the instance is stopped – dynamically allocated
- Used in public subnets
- No charge
- Cannot be moved between instances
- Private IP Address
- retained when the instance is stopped
- Used in public & private subnets
- No charge
- Elastic IP Address
- Static address
- Charged even when you are not used
- Can be moved between instances and ENIs
- Static address